Pentester Academy Free Courses
Pentester Academy Free Courses - Specifically, the windows system programming and kernel programming courses. Classes are held at the tactical security protection academy. Unlimited access to all labs and badge challenges; 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. Please see class options and pricing below. Our online training was designed by law enforcement and educational. Learn how to write and implement python scripts to pentest linux and windows in this free online cybersecurity course. Put yourself in the shoes of an attacker and perform a full penetration test on a web application, using the methods and tools of a professional pentester! Access all free labs, such as our community labs and ctfs; Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. To get started with free access, simply sign. Use these pentester academy free coupon and get pentester academy free courses with 100% off coupons. When you are ready, contact us to sign up for in person training classes. Access all free labs, such as our community labs and ctfs; The tactical security protection academy provides state of the industry, security guard online training in just 20 hours. Please see class options and pricing below. I've been looking at some courses on pentester academy i think i would be interested in. 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Classes are held at the tactical security protection academy. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. When you are ready, contact us to sign up for in person training classes. Unlimited access to all labs and badge challenges; Classes are held at the tactical security protection academy. The tactical security protection academy provides state of the. I've been looking at some courses on pentester academy i think i would be interested in. 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Use these pentester academy free coupon and get pentester academy free courses with 100%. Please see class options and pricing below. Penetration testing, also known as a ‘pen test’ or ‘ethical hacking’, is a cybersecurity approach that aims to identify and access the security loopholes in an organisation. Classes are held at the tactical security protection academy. Learn how to write and implement python scripts to pentest linux and windows in this free online. When you are ready, contact us to sign up for in person training classes. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. Use these pentester academy free coupon and get pentester academy free courses with 100% off coupons. Specifically, the windows system programming and kernel programming courses. Access. Unlimited access to all labs and badge challenges; To get started with free access, simply sign. Specifically, the windows system programming and kernel programming courses. Learn how to write and implement python scripts to pentest linux and windows in this free online cybersecurity course. Put yourself in the shoes of an attacker and perform a full penetration test on a. To get started with free access, simply sign. Please see class options and pricing below. Penetration testing, also known as a ‘pen test’ or ‘ethical hacking’, is a cybersecurity approach that aims to identify and access the security loopholes in an organisation. Learn how to write and implement python scripts to pentest linux and windows in this free online cybersecurity. Use these pentester academy free coupon and get pentester academy free courses with 100% off coupons. Our online training was designed by law enforcement and educational. 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Put yourself in the. I've been looking at some courses on pentester academy i think i would be interested in. The tactical security protection academy provides state of the industry, security guard online training in just 20 hours. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. Access all free labs, such as. Unlimited access to all labs and badge challenges; When you are ready, contact us to sign up for in person training classes. To get started with free access, simply sign. Ready to commence your journey to becoming a certified pentester? Learn how to write and implement python scripts to pentest linux and windows in this free online cybersecurity course. To get started with free access, simply sign. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Ready to. Put yourself in the shoes of an attacker and perform a full penetration test on a web application, using the methods and tools of a professional pentester! Ready to commence your journey to becoming a certified pentester? Learn how to write and implement python scripts to pentest linux and windows in this free online cybersecurity course. Classes are held at the tactical security protection academy. 20hr unarmed security officer training certificate after purchasing, you will have access to work through the lessons below in sequence, and mark complete the lessons and topics as you go. Check out our collection of free resources to learn penetration testing including youtube videos, free courses, blogs, and community support. When you are ready, contact us to sign up for in person training classes. The tactical security protection academy provides state of the industry, security guard online training in just 20 hours. Our online training was designed by law enforcement and educational. Specifically, the windows system programming and kernel programming courses. Please see class options and pricing below. To get started with free access, simply sign. Penetration testing, also known as a ‘pen test’ or ‘ethical hacking’, is a cybersecurity approach that aims to identify and access the security loopholes in an organisation.Pentester Academy Online Courses with Certifications [202425] Edcroma
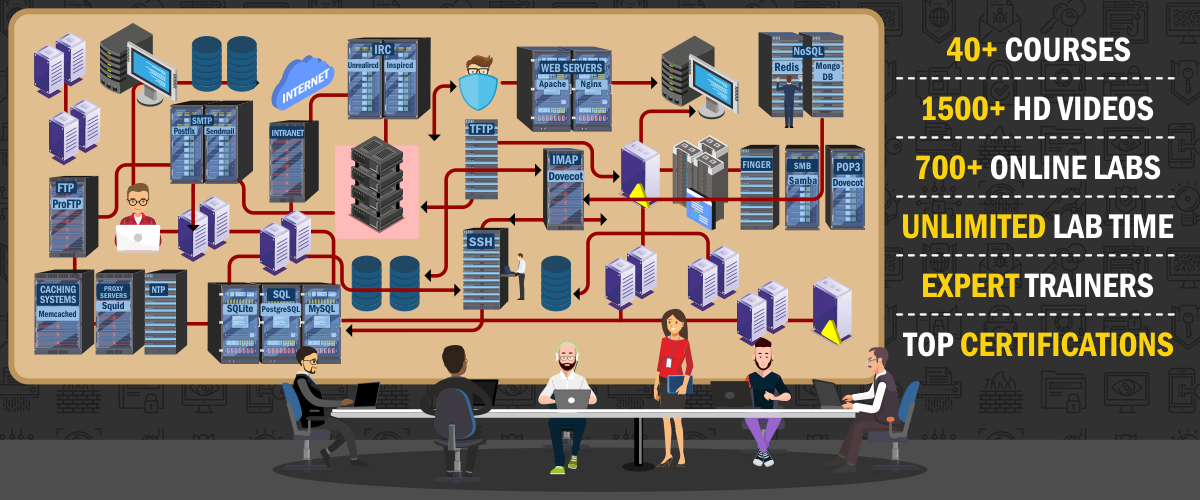
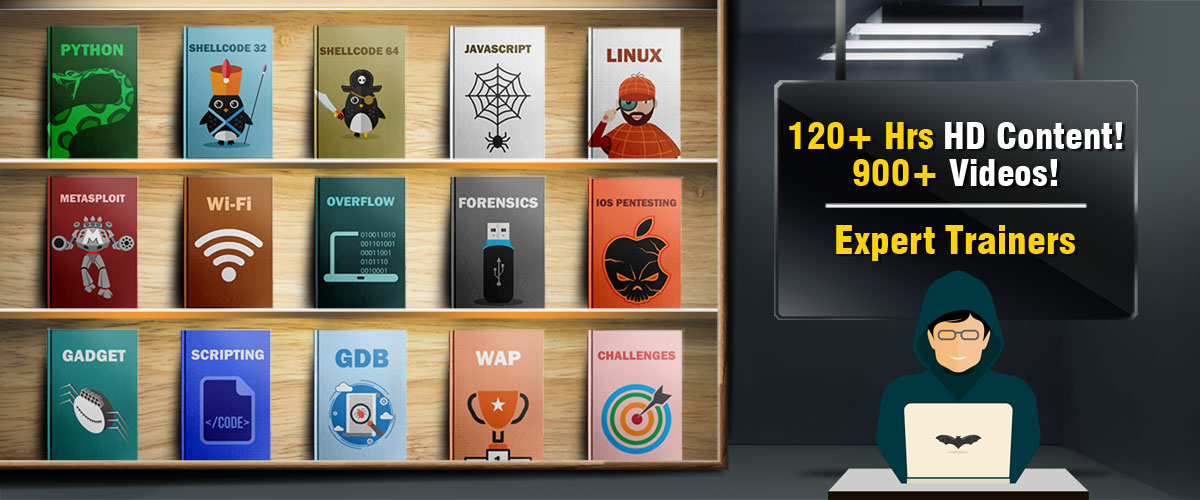
Pentester Academy Learn Pentesting Online
Pentester Academy Learn Pentesting Online
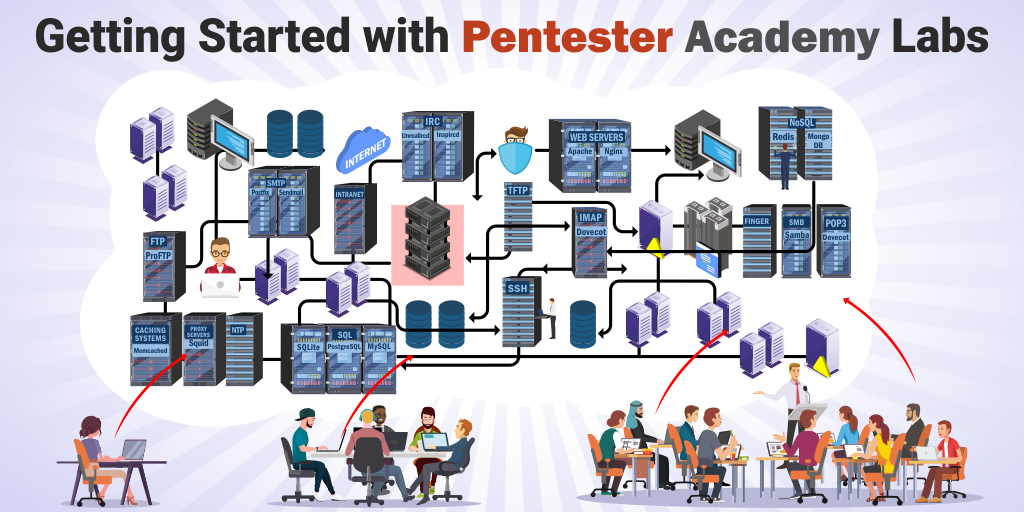
Getting Started with Pentester Academy Labs YouTube
Pentester Academy for Beginners Getting Started with our Labs by
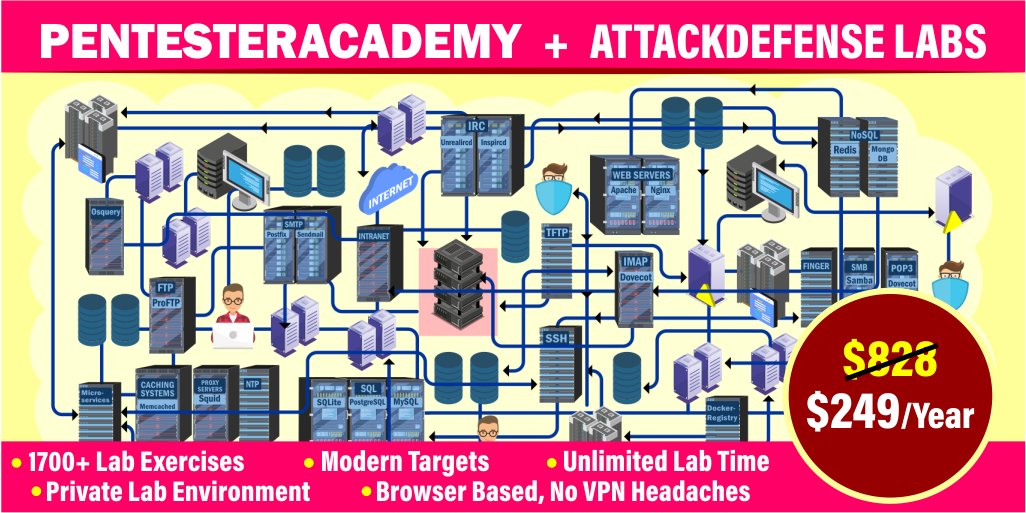
Pentester Academy on Twitter "70 Discount on our annual subscription
Pentester Academy Twitter, Facebook Linktree
Pentester Academy on Twitter "Start learning how pentest with our free
Announcing Pentester Academy Certifications!
Pentester Academy Blog
I've Been Looking At Some Courses On Pentester Academy I Think I Would Be Interested In.
Unlimited Access To All Labs And Badge Challenges;
Use These Pentester Academy Free Coupon And Get Pentester Academy Free Courses With 100% Off Coupons.
Access All Free Labs, Such As Our Community Labs And Ctfs;
Related Post:
![Pentester Academy Online Courses with Certifications [202425] Edcroma](https://edcroma.com/wp-content/uploads/2024/10/logggo-2.png)