Cyber Security Course Outline
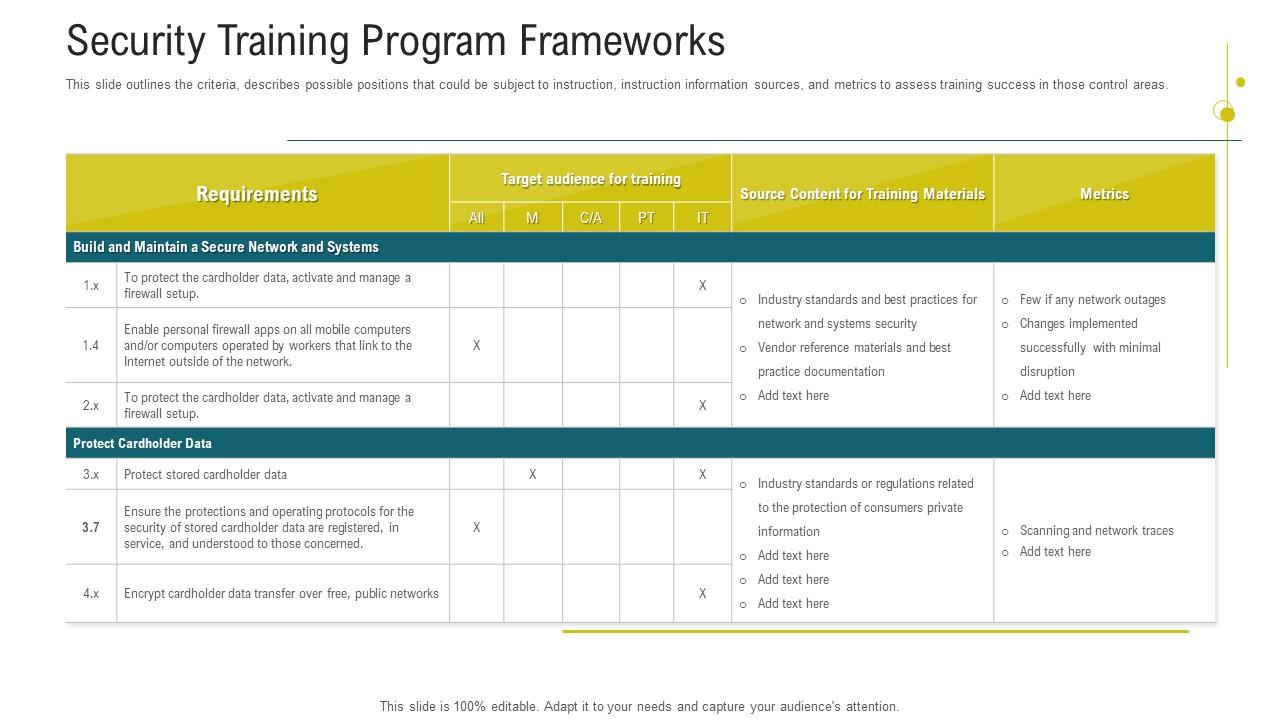
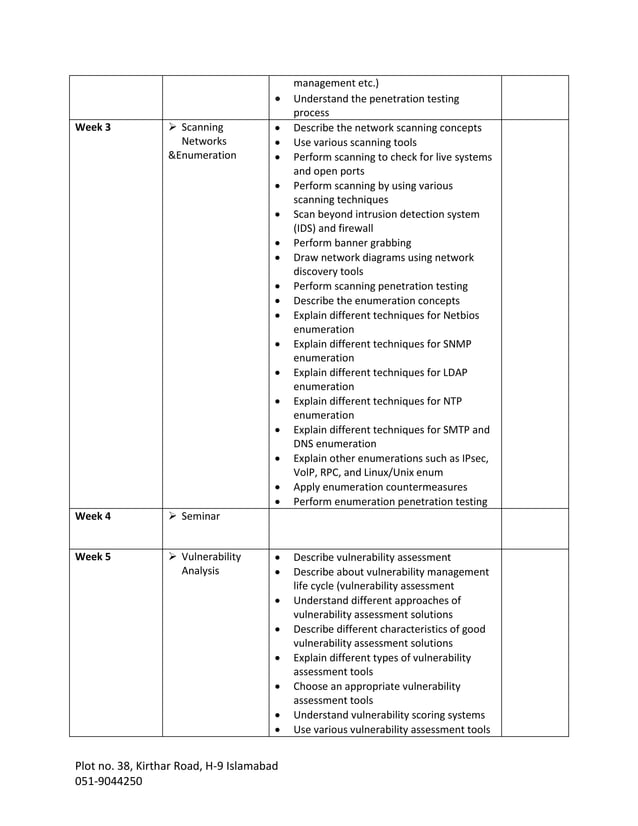
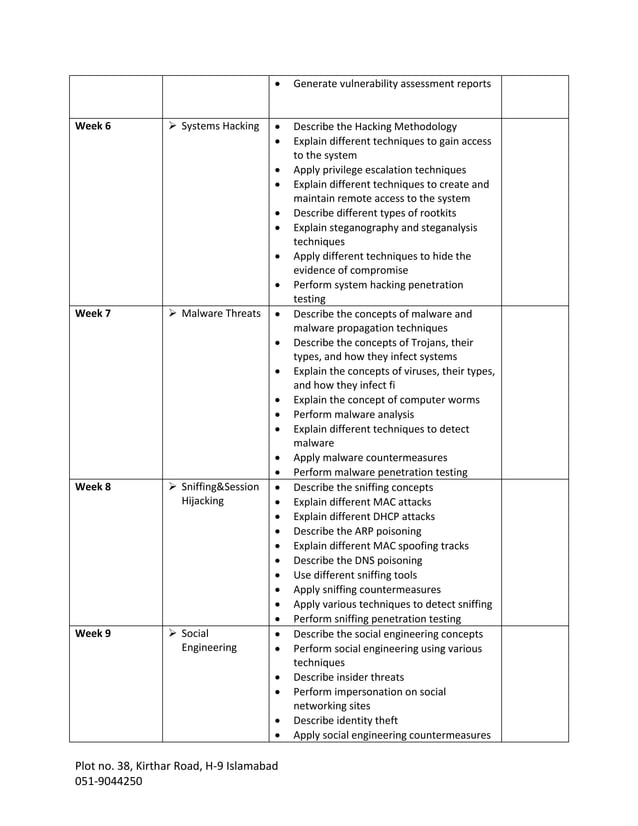
Cyber Security Course Outline - Learn the principles, concepts, issues, and trends of cybersecurity in this online course offered by unsw school of computer science and engineering. Protect yourself and your data: They will better understand the aim of these. Learn how to convey effective defense techniques without being overly suspici. The bachelor of cybersecurity program was designed with the intention for students to progress together in cohorts, registering in the. Outline key network security concepts 1.1 network vulnerabilities that affect cyber security in a data network are defined 1.2 differences between network security and. Principals of cyber security course code: It introduces students to common cyber threats, vulnerabilities, risks related to web applications, networks and software. It covers fundamental topics on the first day such as security principles, laws, and risk management. The course is open until. Outline key network security concepts 1.1 network vulnerabilities that affect cyber security in a data network are defined 1.2 differences between network security and. Protect yourself and your data: Our cybersecurity in information technology certificate of undergraduate study program requires the completion of 12 semester hours (four courses) and can be earned as a separate credential or stacked as part of the bachelor of arts in computer systems technology. The course covers topics such as phishing, malware, password management, social engineering. This semester plan represents an example progression through the major. Learn the principles, concepts, issues, and trends of cybersecurity in this online course offered by unsw school of computer science and engineering. It covers fundamental topics on the first day such as security principles, laws, and risk management. Rself and making others aware of security risks. In the cybersecurity course, students will learn about the practice of protecting networks, systems, and programs from digital attacks. Drawing on kpmg’s global experience, we outline essential preventive measures, and the critical requirements for detecting an incident when it occurs. These courses must be completed by the terms as listed above in the critical tracking criteria. They will better understand the aim of these. Flexible schedule8 & 16 week coursesno cost applicationmonthly starts Rself and making others aware of security risks. The course outline covers topics such as hacking tools, cryptography,. Learn how to keep confidential information secure; Learn how to convey effective defense techniques without being overly suspici. An inside look at coursework. Course wise detailed curriculum / syllabus course name: Discover the complete cybersecurity course syllabus. Below, you will find a list includes a sampling of titles of coursework for the. Discover the complete cybersecurity course syllabus. The bachelor of cybersecurity program was designed with the intention for students to progress together in cohorts, registering in the. It covers fundamental topics on the first day such as security principles, laws, and risk management. We share with. The course covers topics such as phishing, malware, password management, social engineering. This online course will provide theoretical and practical knowledge of it and cyber security and security methods for computer, network and electronic communication. Learn how to convey effective defense techniques without being overly suspici. They will better understand the aim of these. Rself and making others aware of. Varies by country (us$249 for candidates. Not start as a technically sophisticated attack. Our cybersecurity in information technology certificate of undergraduate study program requires the completion of 12 semester hours (four courses) and can be earned as a separate credential or stacked as part of the bachelor of arts in computer systems technology. Below, you will find a list includes. Learn how to prevent, detect and react to cyber attacks with this video training program. Free, exam outline, flashcards, a practice quiz, and a study app; The course is open until. This online course will provide theoretical and practical knowledge of it and cyber security and security methods for computer, network and electronic communication. The course consists of weekly activities,. Our cybersecurity in information technology certificate of undergraduate study program requires the completion of 12 semester hours (four courses) and can be earned as a separate credential or stacked as part of the bachelor of arts in computer systems technology. Not start as a technically sophisticated attack. Free, exam outline, flashcards, a practice quiz, and a study app; In the. An inside look at coursework. Principals of cyber security course code: Learn how to keep confidential information secure; The course outline covers topics such as hacking tools, cryptography,. They will better understand the aim of these. Below, you will find a list includes a sampling of titles of coursework for the. The objective of the course is to prepare trainees to work as information security professionals. The course covers topics such as phishing, malware, password management, social engineering. Varies by country (us$249 for candidates. The course consists of weekly activities,. Outline key network security concepts 1.1 network vulnerabilities that affect cyber security in a data network are defined 1.2 differences between network security and. Understand topics, practical projects, & necessary skills to learn to become a proficient ethical hacker. Learn the principles, concepts, issues, and trends of cybersecurity in this online course offered by unsw school of computer science and. In the cybersecurity course, students will learn about the practice of protecting networks, systems, and programs from digital attacks. The course is open until. Not start as a technically sophisticated attack. Flexible schedule8 & 16 week coursesno cost applicationmonthly starts Discover the complete cybersecurity course syllabus. Transition your career into cyber security course outline pdf with practical training, industry certification, and job placement. Here is why cybersecurity courses are worth considering: Learn how to keep confidential information secure; Learn how to prevent, detect and react to cyber attacks with this video training program. This semester plan represents an example progression through the major. Varies by country (us$249 for candidates. It introduces students to common cyber threats, vulnerabilities, risks related to web applications, networks and software. An inside look at coursework. Our cybersecurity in information technology certificate of undergraduate study program requires the completion of 12 semester hours (four courses) and can be earned as a separate credential or stacked as part of the bachelor of arts in computer systems technology. Rself and making others aware of security risks. Understand topics, practical projects, & necessary skills to learn to become a proficient ethical hacker.Cybersecurity Awareness Training Security Training Program Frameworks
Cyber Security Course Outline PDF Malware
Cyber Security Staff Awareness Course (Group Course) CCoE
Cybersecurity Fundamentals Course Outline Computer Security Security
Cyber Security Expert Course 2021 Cyber Security Course Cyber
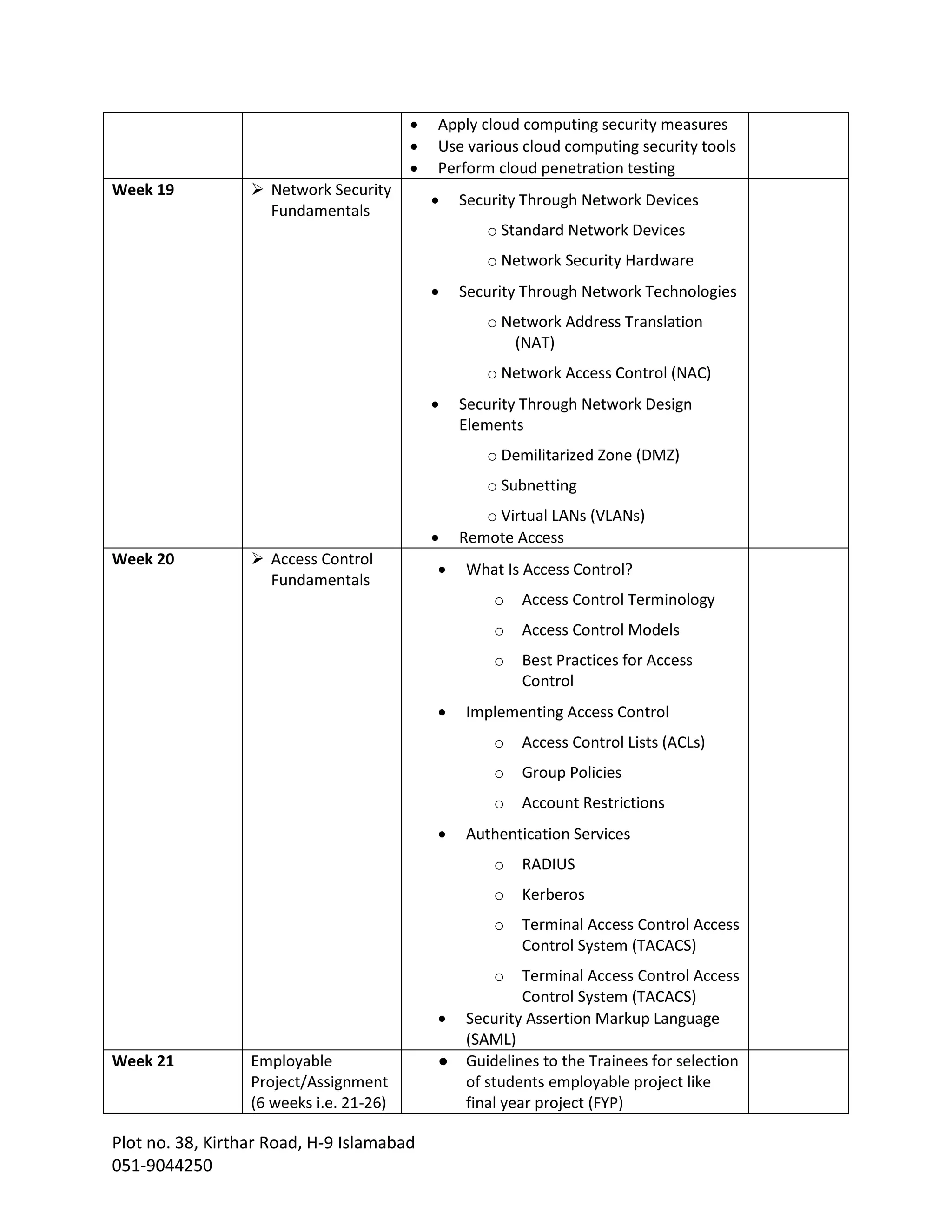
cybersecurity course outline PDF
cybersecurity course outline PDF
cybersecurity course outline PDF
cybersecurity course outline PDF
Cyber Security Course Outline CES LUMS PDF Security Computer
These Courses Must Be Completed By The Terms As Listed Above In The Critical Tracking Criteria.
The Objective Of The Course Is To Prepare Trainees To Work As Information Security Professionals.
What Are The Benefits Of Cybersecurity Courses?
The Bachelor Of Cybersecurity Program Was Designed With The Intention For Students To Progress Together In Cohorts, Registering In The.
Related Post: